Seguridad de la Información y Criptografía
Homework 6 - Report 2
Homework 6 - Report 2
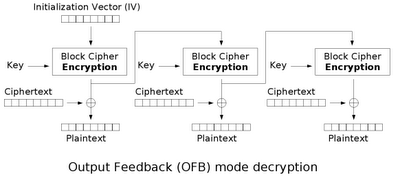
The Output Feedback (OFB) mode is a confidentiality mode that requires a unique initialization vector for every message that is ever encrypted under the given key. [1]
The Federal Data Encryption Standard (DES) specifies a crypto-graphic algorithm to be used for the cryptographic protection of sensitive, but unclassified, computer data. This FIPS defines four modes of operation for the DES which may be used in a wide variety of applications. The modes specify how data will be encrypted and decrypted. The modes included in this standard are the Electronic Codebook (ECB) mode, the Cipher Block Chaining (CBC) mode, the Cipher Feedback (CFB) mode, and the Output Feedback (OFB) mode. [2]
This standard is based on the DES and provides the next level of detail necessary for providing compatibility among DES equipment. This standard anticipates the development of a set of application standards which reference it such as communication security standards, data storage standards, password protection standards and key management standards. Cryptographic system designers or security application designers must select one or more of the possible modes of operation for implementing and using the DES in a cryptographic system or security application. [3]
The Output Feedback mode was created by Computer Systems Laboratory and the standard was registered by the National Institute of Standards and Technology.
Difference between the others
The Output feedback has some similarities to the ciphertext feedback mode in that it permits encryption of differing block sizes, but has the key difference that the output of the encryption block function is the feedback, instead of the ciphertext. The XOR value of each plaintext block is created independently of both the plaintext and ciphertext. It is this mode that is used when there can be no tolerance for error propagation, as there are no chaining dependencies. Like the ciphertext feedback mode, it uses an initialization vector. Changing the IV in the same plaintext block results in different ciphertext.
How it works?
The kind of mathematics that this method use is XOR operation, and is the reason why we use the same operation to encrypt and decrypt.
$C_j = P_j \oplus O_j$
$P_j = C_j \oplus O_j$
$O_j = E_k(I_j)$
$I_j = O_{j-1}$
$I_0 = IV$
How to encrypt:
http://upload.wikimedia.org/wikipedia/commons/a/a9/Ofb_encryption.png
How to decrypt:
http://upload.wikimedia.org/wikipedia/commons/8/82/Ofb_decryption.png
We can see in the images that each output feedback block cipher operation depends on all previous ones.
Example
This is a simple example of the output feedback implemented in a python script.
ramon@pavilion:~/Documents$ python outputfeedback.py Text: me gusta la clase de cripto Key: abcdefgh IV: 12345678 Block size: 8 Block #1 Input block: 12345678 Output block: rtvxz| " Plaintext: me gusta Ciphertext: a[vaqqtc Decrypted: me gusta Block # 2 Input block: rtvxz| " Output block: UX[^adgj Plaintext: la clas Ciphertext: UF>^FRJ_ Decrypted: la clas Block # 3 Input block: UX[^adgj Output block: 8<@DHLPT Plaintext: e de cri Ciphertext: }<&+H1D? Decrypted: e de cri Block # 4 Input block: 8<@DHLPT Output block: y %*/49> Plaintext: pto Ciphertext: +05:?&// Decrypted: pto Text: me gusta la clase de cripto
What I did in my program?
- First my program divide the text in blocks.
- Then, I use the Input Vector only for the first iteration to get the output block using the key.
- Using the output block, I encrypt the text block.
- I get the encrypted text block.
- In this case, I used the encrypted block text to decrypted at the same time, but it must be separately.
- Then I use the last output block, for the new input block, and repeat the last steps, until we don't have more text blocks.
- At the end, I print all the decrypted text block together.
Vulnerabilities
In terms of error correction, output feedback can tolerate ciphertext bit errors, but is incapable of self-synchronization after losing ciphertext bits, as it disturbs the synchronization of the aligning keystream. A problem with output feedback is that the plaintext can be easily altered, but using a digital signature scheme can overcome this problem.
References:
[1] - Block Cipher Modes of Operations
[2] [3] - Standard for DES - Modes of Operation
Definition - Output Feedback
OFB - Examples

Bien; 7.
ResponderEliminar